“Nonzero:” On Evidence-Based Investigations and Rudy Giuliani’s Devices
After the WaPo published its 8,000-word story purporting to describe the January 6 investigation, and after I pointed out key gaps and problems with it, Carol Leonnig reached out to me to find out why I found WaPo’s silence about Rudy Guiliani’s devices so problematic.
Even after my post, Leonnig still understood the exploitation of Rudy’s devices to be limited to the FARA investigation out of SDNY. “I hear you re search of Rudy phones but to be clear that is for probe of lobbying law violations – not a plan to look at Trump orbit plot to overturn elex results,” she described.
To be clear: Her understanding was correct with regards to the known warrant used to seize Rudy’s devices. It was badly wrong with regards to the process used to review them, something that has been public for a long time.
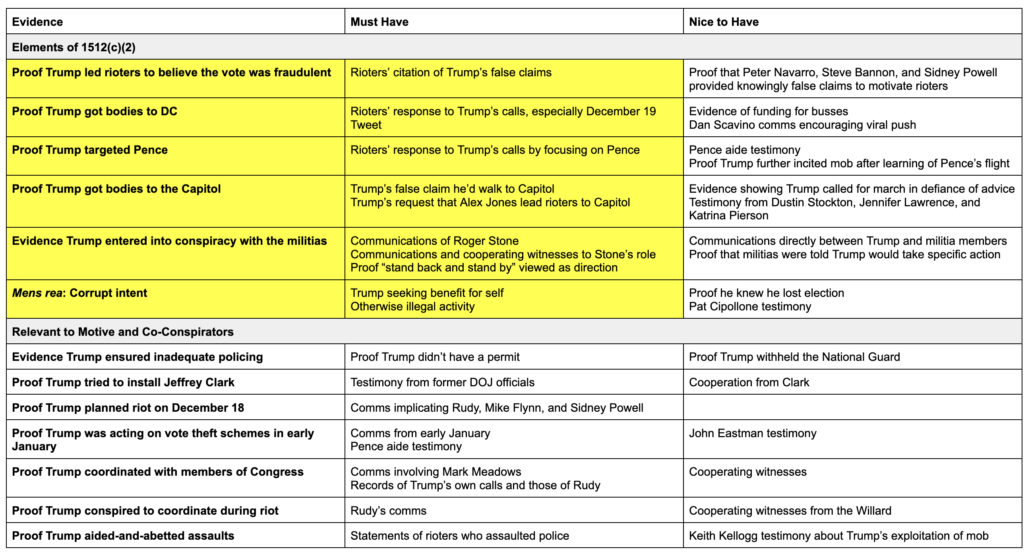
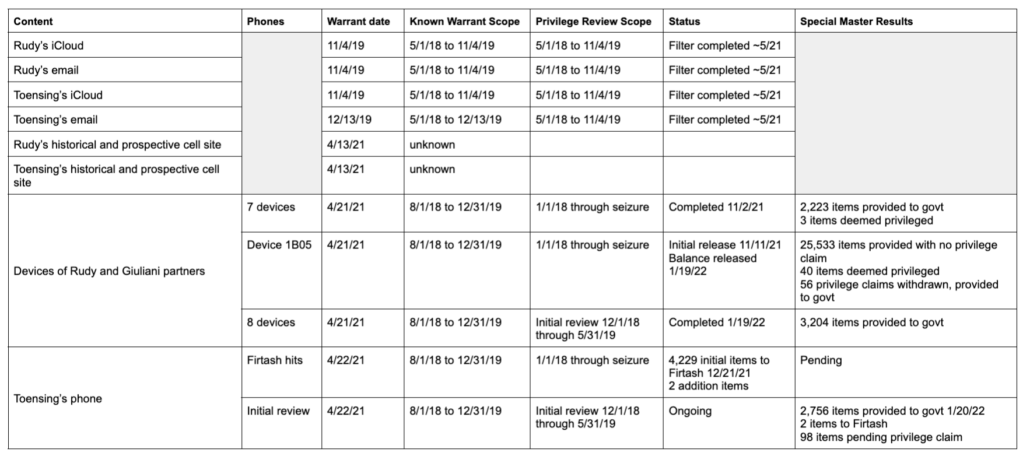
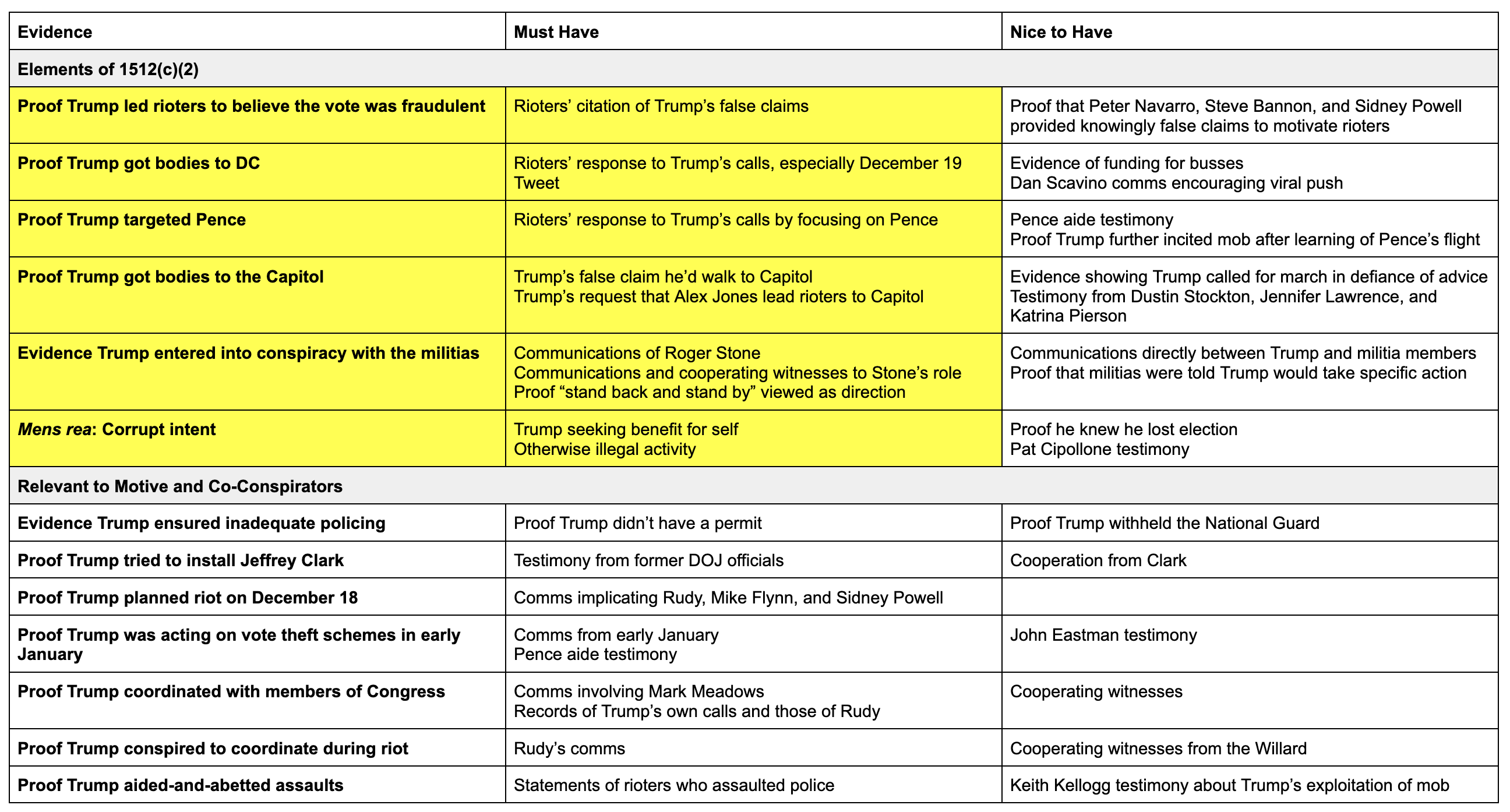
As I first laid out over 18 months ago, after seizing Rudy’s devices, SDNY successfully requested that the Special Master process review everything on Rudy’s devices between January 1, 2018 through the date of seizure, irrespective of scope:
- April 21, 2021 (Lisa Monaco’s first day on the job): DOJ approved a warrant for Rudy’s devices in SDNY FARA investigation
- April 29, 2021 (the day after seizure): Citing the Michael Cohen case, SDNY asked Judge Paul Oetken to appoint Special Master
- August 18, 2021: Special Master Barbara Jones notices a dispute about the range of privilege review, sets schedule for briefing
- September 3, 2021: SDNY generously offers to limit Special Master review to files post-dating January 1, 2018 through date of seizure
- September 16, 2021: Judge Oetken rules that the Special Master shall review for privilege all content between January 1, 2018 and date of seizure
Oetken’s decision pertained to more than just timeline. It made clear that the government would conduct any responsiveness review.
First, this Court appointed the Special Master for the purposes of reviewing the materials for privilege, not for responsiveness. While a general exclusion [of material that pre-dated January 1, 2018] as proposed by the Government is appropriate, the imposition of detailed date restrictions or other responsiveness criteria would risk further delay in the review process.
Second, the warrants themselves do not contemplate that an arm of the Court, rather than Government investigators, would conduct a review of the warrant materials for responsiveness, nor is the Court aware of any legal authority mandating such review. To be sure, as the Government acknowledges, the warrants must be executed according to their terms. But the fact that the Court has appointed a Special Master for privilege review in this circumstance does not dictate that such review be expanded to review for responsiveness.
Once this Special Master privilege review finished, then, any content responsive to any probable cause warrant targeting those devices would be available to the government without further privilege review.
Note, when DOJ suggested Barbara Jones to serve as Special Master in Trump’s Florida Special Master matter last September, Trump raised a specific and secret objection to her, though he had raised no such objections after her review of Michael Cohen’s devices in 2018.
Based on that series of decisions — starting with a decision made on Lisa Monaco’s first day, followed by a successful argument that prosecutors, not a Special Master, would do any scope review for responsiveness with warrants (the reverse process as used for James O’Keefe’s phone) — DOJ guaranteed that the January 6 investigation could immediately access Rudy’s content, either based off a plain view discovery of evidence pertaining to a crime (which is how the investigation into Michael Cohen evolved from a FARA investigation to include the hush money payment that is the basis of Alvin Bragg’s indictment), or later warrants obtained as the January 6 investigation progressed. If DOJ obtained a new January 6 specific warrant, Rudy — and any journalists he wanted to complain to — would get no notice, because (as happened repeatedly in the Cohen investigation) the new warrant would be served internally.
DOJ secured the availability of Rudy’s content (pending a new warrant) by September 2021, before Matthew Graves was confirmed and before Thomas Windom was brought in to head up an investigation focusing on Trump’s people, personnel changes that WaPo claims drove the renewed focus on Trump.
In its 8,000-word piece, WaPo raised legitimate concerns about evidence being deleted as DOJ investigated. But within a week of Monaco’s start date, DOJ had preserved the content of Rudy’s devices and started a process that would eventually make it easier for January 6 investigators to access it.
To be sure, we don’t know when or how (via plain view or via a January 6 specific warrant) Rudy’s content was shared with January 6 investigators.
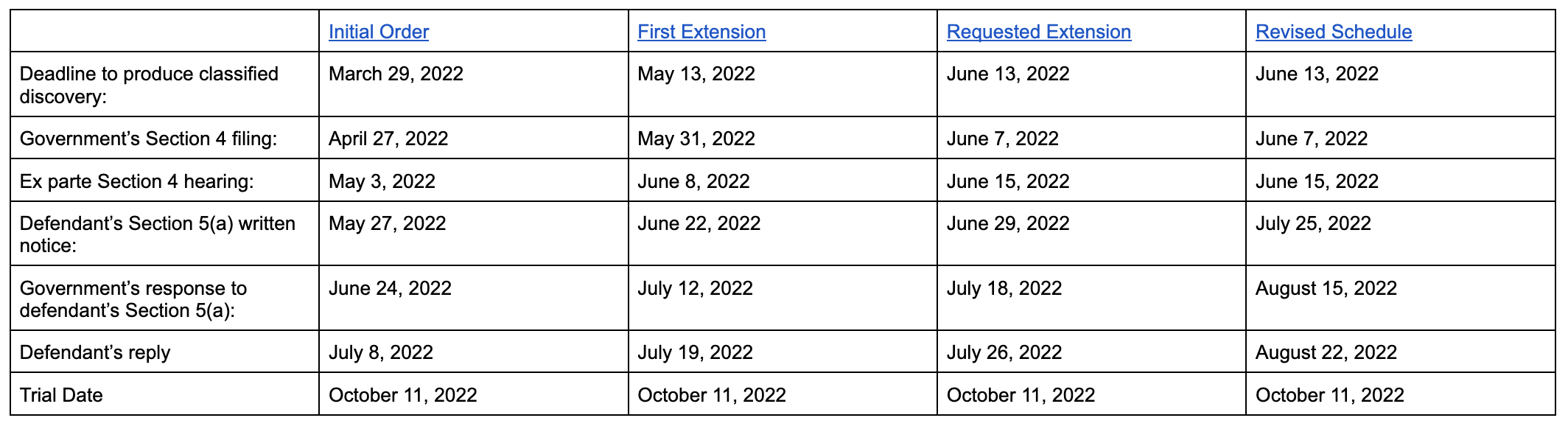
We do know that Special Master Jones prioritized the content on phones that were in current use in April 2021. The first 8 devices she reviewed all included content through seizure. This table shows all the content known to be seized by SDNY; the red rectangle shows the devices, clearly including Rudy’s main phone, Device 1B05, that were reviewed through seizure date.
And, to the limited extent that a sworn declaration from Rudy is reliable, we know that the devices Jones reviewed included all of Rudy’s January 6 content. According to a declaration Rudy submitted in the Ruby Freeman lawsuit, seven of those personal devices seized using a warrant obtained on Lisa Monaco’s first day included all the digital content pertaining to January 6 in his possession at the time.
Apple iPhone 11 ProMax
Apple MacBook Model A22251
Apple iPhone 11 Pro Max
Apple iPad Model: A1709
Apple iPad Model: A2013
Blackberry Model: RGVI6ILW
Apple iPad Model: A1395
[snip]
The TrustPoint One documents consist of all documents that were extracted from the electronic devices taken by the DOJ in April 2021 when the DOJ seized those devices.
The content from the first seven of devices Rudy was currently using was shared with SDNY by November 2, 2021, still before Graves was sworn in as US Attorney in DC. Jones started turning over content from what appears to be Rudy’s main phone on November 11, 2021, with the balance turned over on January 19, 2022.
Again, this information would have been turned over to SDNY, not DC USAO, and we don’t know when and via what means January 6 related content got passed on to DC. But whenever it was, it was available because of decisions made well before WaPo’s timeline, decisions that would have involved approval from people WaPo described as “slow” and “cautious.”
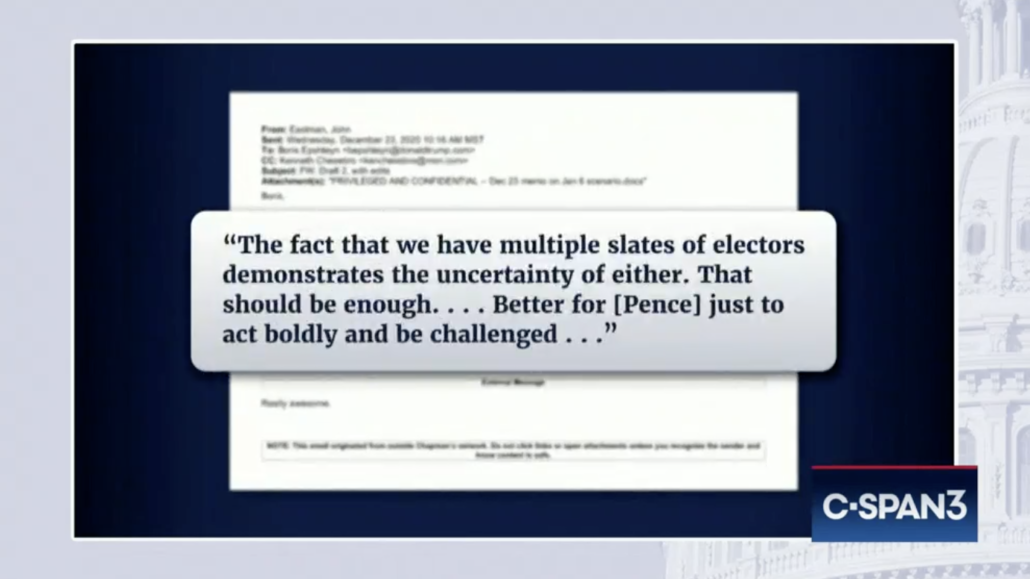
Whatever else it did, the way DOJ did the Special Master review of Rudy’s devices shaved nine months off any investigation pertaining to Trump’s personal lawyer, one of the most central players in Trump’s coup attempt, because whenever DC developed probable cause to access that content, the privilege review would already be done. By comparison, the privilege review for John Eastman and Jeffrey Clark’s content began on June 17, 2022, and NYT describes that privilege reviews of people like Mark Meadows and Cleta Mitchell started after July 2022.
One reason it is likely that Rudy’s content — and not just pressure generated in January 2022 from the January 6 Committee, as WaPo quotes an anonymous source claiming — drove the fake electors investigation is the focus of the investigation. The first fake elector warrants sent in May 2022 (not June, as WaPo implies) as well as those sent in June and November all included Victoria Toensing and Joe DiGenova. Rudy’s known interviews always list the couple as key members of his post-election team. But no one else seems to have cared or figured out what they did. After Rudy listed them in his January 6 interview, the Committee never once raised them again.
Q. Who was on your team at that point [November 5]?
A. You know, it was put out in a press release some days later. So it’s hard to know exactly who joined. Very early on, there was Jenna Ellis, Vicki Toensing, Joseph DiGenova, Boris Epshteyn. That was the main team. We were joined by Christian Bobb about 5 days later, and by — by Katherine Friess, maybe 3 or 4 days later.
So if you look at the list of the team — now, it took about — that was the original team, meaning in the first 3, 4, 5 days. Within about a week or two, I can give you all the names if you want them.
Q. Who else joined the team after that group you just mentioned, lawyers? I’m just talking about lawyers for the moment.
A. Just lawyers, okay. So Toensing, DiGenova, Bob[b], Friess, Ellis, Epshteyn.
Neither appears to have been interviewed; neither is mentioned in the final report. Nor did they get much focus in the investigation. Christina Bobb and Eric Herschmann mentioned them in passing. Sidney Powell described that they may have been at a White House meeting on November 8. Alex Cannon was asked about an urgent demand that the campaign provide Toensing with a paralegal on November 29. Jacqueline Kotkiewicz, a campaign researcher, described doing at least one project for Toensing, the only substance of which that she could remember was a fight over whether “nonzero” meant “zero” or “a number greater than zero.” Cleta Mitchell described connecting Toensing with John Eastman and admitted having, “quite a number of calls with Victoria,” but couldn’t remember the substance. According to an email Mitchell reviewed, Toensing then shared Eastman’s whack theories with state legislators.
Nothing that came from the January 6 Committee explains why Toensing and DiGenova would be a persistent focus of DOJ’s fake electors investigation. But they were. (As I have noted, Boris Epshteyn and Bernie Kerik were also a focus of DOJ subpoenas before they were mentioned in J6C coverage, but unlike Toensing and DiGenova, they soon became a public focus of J6C.)
As far as is public, Toensing’s phone, which was seized in the same week as Rudy’s devices, was only reviewed for the period covered by the FARA warrants, ending in 2019 (though the content would have been preserved if DOJ ever later had an interest that post-dated that). Additionally, she belatedly invoked spousal privilege over all communications on her seized phone with DiGenova.
But Rudy’s phones — or possibly even the Sidney Powell prong of the investigation that was overt by September 2021, another thing WaPo doesn’t mention — might explain why DOJ’s fake elector investigation doesn’t look like the version that got told in the press or the one told by the January 6 Committee, starting a month later.
There’s one other thing. As I laid out here, Ruby Freeman’s lawyers are pursuing further testimony from Kerik, who served as Rudy’s chief investigator after the election. They’re contesting the privilege claims Kerik has sustained from J6C, based off an argument that Kerik’s communications were not created as work product in anticipation of litigation. As Rudy explained to J6C, his team abandoned the plan to sue to overturn the vote after about the first week post-election in favor of going to legislatures, so any work product Kerik created would have been in anticipation of legislative hearings, not litigation. As stated in emails exchanged between lawyers, Rudy is not claiming privilege over Georgia-related work product done in anticipation of sharing information with legislatures (as distinct from litigation).
The position we took was that communications and work product in connection with presenting testimony and evidence before the Georgia Legislature in December 2020 was not privileged. Not that it was privileged but that we were waiving it.
[snip]
I would say that any communications or materials created in anticipation of the December 2020 Georgia Senate hearings are not privileged and should not be withheld.
Rudy had claimed similar communications were privileged in his January 6 Committee deposition given in May 2022, so this is a change in stance.
There are a lot of things that have happened since that could explain the changed posture. A different lawyer, Joe Silbey, is handling Rudy’s civil challenges. Rudy testified last August in Fani Willis’ investigation. Beryl Howell issued a ruling on the application of privilege before her on May 19 of this year (the latter of which Freeman’s lawyers cited in discussions with Kerik lawyer Tim Parlatore). But another possible explanation for Rudy’s willingness to share information on pressuring legislatures when he hadn’t before would be if the material had been deemed non-privileged in the past, perhaps one of the 56 documents on Rudy’s phone over which an initial privilege claim was either withdrawn or overridden.
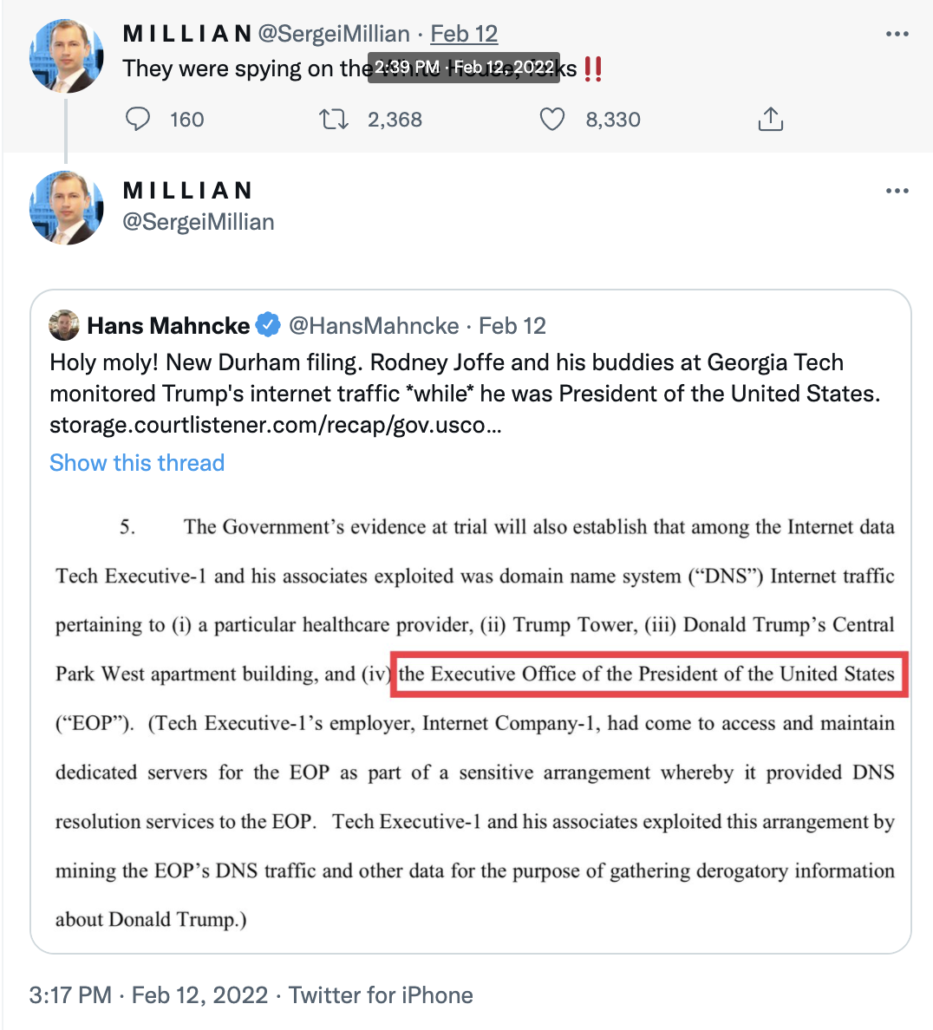
To the extent it presents a coherent timeline, WaPo’s story largely tells when former FBI Assistant Director Steve D’Antuono vetoed DOJ requests and when formal investigative decisions were made. But such formal decisions always follow evidentiary collection, often by months. That’s especially true here; it’s what Merrick Garland and Lisa Monaco demanded. Even with Stewart Rhodes, whose prosecution this story makes a far more central part of January 6 than Rhodes’ actions merit, this story doesn’t talk about known evidence and cooperating witnesses that advanced the investigation (not even Joshua James, the sole witness who would play a function in WaPo’s narrative). The only mention — at all — of evidence that might drive such decisions describes J6C investigator Timothy Heaphy sharing information about Trump pressuring Pence and others.
But the January 6 fake electors investigation does not resemble the DOJ one, certainly not as to the relative import of Toensing and DiGenova.
The most obvious place that focus might have come from, and come from in time to shape the May 2022 subpoenas, would be Rudy’s phones — phones that DOJ started the process of exploiting well before J6C even started investigating.
Update: Fixed an error re: Matthew Graves’ timeline. He was confirmed on October 28, 2021 but sworn in on November 5. So SDNY started obtaining Rudy’s content before Graves was sworn in.